Custody Models Used in Real-World Asset Tokenization: Critical Safeguard Frameworks
This article is part of the broader Real-World Assets educational framework, examining the five custody models used in real-world asset tokenization and the institutional safeguard architecture that determines whether digital ownership is legally enforceable or merely a string of code pointing to nothing.
Educational Notice
This article is provided for informational and educational purposes only. It does not constitute financial, legal, or investment advice. Custody structures and regulatory requirements vary by jurisdiction and asset classification. Professional legal consultation should be obtained before engaging with any tokenized asset structure.
Introduction: The Vault and the Key
Digital ownership is only as strong as the vault protecting the underlying physical asset. In real-world asset tokenization, it helps to separate two distinct things: the Key (the digital token you hold, representing your ownership rights) and the Vault (the legal and physical safeguarding infrastructure protecting the actual asset those rights are tied to).
If the vault is weak, your digital key is worthless. A token without sound custody infrastructure behind it is just code pointing to nothing. This is why custody models used in real-world asset tokenization are not optional infrastructure. They are the foundation everything else depends on.
Understanding custody models is essential to evaluating ownership security, legal enforceability, and institutional trust in any tokenized system. While tokenization creates a blockchain-based digital representation of ownership, custody safeguards the underlying asset and the legally enforceable ownership rights tied to it, ensuring that digital tokens remain anchored to real-world value.
If you are new to tokenization fundamentals, these articles provide useful context:
- What Is Asset Tokenization? A Beginner-Friendly Explanation
- How Real-World Asset Tokenization Works Step by Step
- Real-World Asset Tokenization Explained
The Bank for International Settlements (BIS) has highlighted institutional safeguards as central to financial infrastructure modernization. Digital ownership is only as reliable as the custody infrastructure protecting the underlying asset.
In Simple Terms: What Are Custody Models in RWA Tokenization?
Custody models used in real-world asset tokenization define who is responsible for safeguarding the underlying asset or ownership documentation associated with tokenized ownership. Three principles apply to every model:
- Tokenization records ownership digitally on a blockchain
- Custody protects the physical or legal asset and preserves enforceability
- Verification ensures alignment between the legal and digital systems
Custody is not optional infrastructure. It is foundational. Without it, the digital ownership record has nothing real behind it.
What Do Custody Models Actually Govern?
Custody models used in real-world asset tokenization are institutional frameworks that determine who holds or supervises the underlying asset, how ownership documentation is protected, how asset continuity is preserved through events such as platform failure, and how digital tokens remain legally enforceable.
In traditional finance, custody refers to safeguarding financial instruments held on behalf of clients. In tokenized systems, custody extends further: it encompasses physical asset supervision, legal registry oversight, documentation integrity, ownership isolation structures, and audit and verification mechanisms. The U.S. Securities and Exchange Commission (SEC) has emphasized the importance of digital asset custody safeguards in maintaining market integrity.

The 5 Custody Models: From Basic to Institutional Grade
Level 1: Direct Custody Model
In the direct custody model, the tokenization provider maintains operational custody of the underlying asset. A single entity is responsible for both asset custody and tokenization, with integrated ownership and operational control under unified documentation and supervision.
This creates a significant Single Point of Failure. If the platform goes bankrupt, is hacked, or ceases operations, the assets are at risk because there is no independent party holding them separately. This model may be appropriate when the tokenization provider holds legal authority and regulated custody capability, but it carries higher concentration risk and greater reliance on internal governance controls. It is generally suitable for early-stage or experimental platforms, not for institutional capital.
Level 2: Third-Party Institutional Custody Model
In this model, custody responsibilities are fully segregated from the tokenization platform. An independent custodian safeguards the asset while the tokenization platform manages digital ownership separately. This Segregation of Duties (the institutional principle of separating asset control from asset administration) is the bedrock of modern finance and the standard expected by professional investors.
The key concept here is the Qualified Custodian (a term referring to SEC-licensed or equivalently regulated financial institutions, such as licensed banks or broker-dealers, that are legally permitted to hold client assets on their behalf). Institutions such as BNY Mellon and State Street operate as Qualified Custodians in traditional finance. For tokenized real estate, the equivalent is a licensed third-party firm holding the property title documentation independently from the tokenization platform.
Even if the tokenization platform disappears entirely, the asset remains with a regulated, independent custodian. This separation significantly reduces operational concentration risk. The World Bank has emphasized institutional safeguards as essential to financial system resilience.
Level 3: SPV-Based Custody Model
The SPV (Special Purpose Vehicle, a separate legal entity created specifically to hold one asset) custody model isolates ownership within a dedicated legal entity. The SPV holds legal title to the asset. Token holders hold economic rights in the SPV. Ownership is separated from the operational infrastructure of the tokenization platform.
The most important benefit of this structure is Bankruptcy Remoteness (the legal principle that assets held inside the SPV cannot be claimed by creditors of the parent platform if the platform becomes insolvent). The SPV is legally ring-fenced from the platform’s debts. This is the global standard for structured finance and asset-backed frameworks. For detailed analysis of SPV structures, see Legal Structures Behind Tokenized Real Estate.
Level 4: Legal Registry Custody Model
The legal custody model relies on jurisdictionally recognized ownership registries as the authoritative ownership record. Enforceability is derived from statutory frameworks rather than physical possession. Custody is anchored in legal recognition by a government authority. This model is common in securities markets where clearing systems and registries maintain ownership records.
A critical concept here is the Golden Record: when a blockchain record and a government land registry disagree about who owns an asset, the legal registry is the authoritative source of truth. The blockchain is a digital representation. The Golden Record is the legal deed. Tokenization platforms must ensure their on-chain data is perfectly Synchronized with the official government registry at all times. When Synchronization Risk arises (the gap between what the blockchain records and what the official registry holds as the Golden Record), the legal registry always prevails in a court of law.
Level 5: Hybrid Layered Custody Model
Hybrid custody combines multiple safeguards to eliminate every possible Single Point of Failure. It may include legal registry custody, an independent Qualified Custodian, an SPV ownership structure providing Bankruptcy Remoteness, and blockchain record verification. The result is multi-layer risk distribution, enhanced auditability, and reduced single-point failure exposure.
Hybrid models also address the digital key custody dimension through Multi-Sig (Multi-Signature, a wallet security model requiring approval from multiple independent parties before any token transfer can be executed) wallets or MPC (Multi-Party Computation, a cryptographic method that distributes private key control across multiple independent parties so no single person ever holds the complete key) architecture. These ensure that no individual can move the digital tokens without coordinated approval from multiple independent guardians.
Hybrid models reflect institutional-grade infrastructure design. The European Securities and Markets Authority (ESMA) has examined distributed ledger systems within regulated financial markets and emphasized the importance of layered governance safeguards. For verification mechanisms that complement hybrid custody, see What Is Proof of Reserve and On-Chain Transparency Explained.
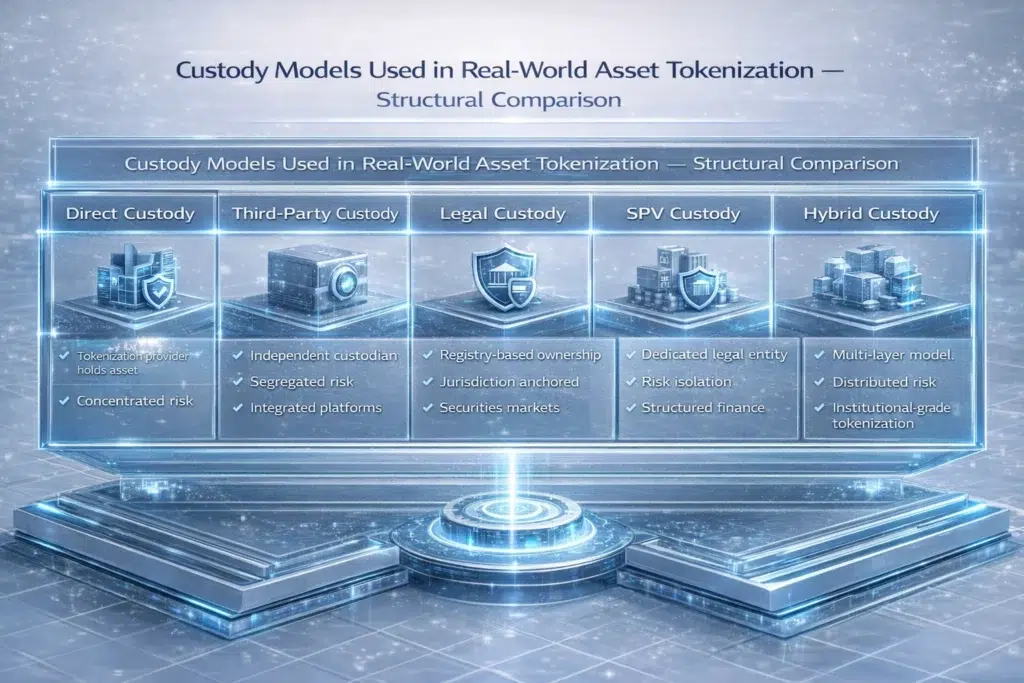
Custody Model Comparison
The five models differ significantly in who holds authority over the asset, how risk is distributed, and what investor profile each is suited to. The table below maps these differences directly.
| Custody Model | Safeguard Strategy | Primary Risk | Who Holds Asset | Suited For |
|---|---|---|---|---|
| Direct | Internal control by the platform | Platform failure creates total loss of access | Tokenization provider | Early-stage |
| Third-Party | Segregation of Duties via Qualified Custodian | Custodian solvency and oversight quality | Independent licensed custodian | Professional investors |
| Legal Registry | Golden Record anchored in statutory law | Synchronization Risk between blockchain and registry | Government registry | Securities markets |
| SPV-Based | Bankruptcy Remoteness via ring-fenced entity | Legal structuring gaps in SPV documentation | Dedicated SPV legal entity | Structured finance |
| Hybrid | Multi-layered: SPV, Qualified Custodian, Multi-Sig | Systemic complexity and coordination across layers | Multiple independent parties | Institutional grade |
Applied Example: Tokenized Commercial Real Estate
Consider a tokenized commercial property using a hybrid institutional custody approach. A legal registry confirms property ownership as the Golden Record. An SPV holds legal title, providing Bankruptcy Remoteness from the platform. A Qualified Custodian (a licensed third-party institution) supervises the title documentation independently. Tokens represent ownership units in the SPV. Blockchain records token transfers with programmable compliance checks. Independent auditors verify documentation alignment between the blockchain records and the legal registry. Multi-Sig wallet architecture ensures no single party can move digital tokens without coordinated approval.
Custody ensures that digital ownership remains legally anchored at every layer. For further verification architecture context, see Who Verifies Real-World Assets in Tokenized Systems?
Why Custody Infrastructure Is Essential
Institutional trust depends on clear ownership linkage, secure asset supervision, legal enforceability, and independent verification. Without all four, the digital token becomes unreliable as a representation of value. Technology alone cannot substitute for institutional safeguards. The vault must be as secure as the key is portable.
Risks and Governance Considerations
Even well-structured custody models carry risk considerations that must be understood and actively governed.
Concentration Risk arises when a single entity controls both the tokenization and the asset custody, creating a Single Point of Failure. Jurisdictional Risk reflects the reality that legal custody frameworks differ significantly across regions. Custodian Solvency Risk exists even with third-party models: independent custodians must be financially stable and themselves subject to regulatory oversight.
Documentation Integrity Risk is perhaps the most underappreciated: incomplete or inconsistent records weaken ownership enforceability regardless of how sophisticated the technology layer is. Synchronization Risk (the gap between what the blockchain records and what the official legal registry holds as the Golden Record) must be actively monitored and immediately corrected when discrepancies arise. Governance frameworks mitigate these risks, but they must be codified in legal documents, not just assumed from technical design.

The 3 Rules of Safe RWA Custody
Before evaluating any tokenized real-world asset structure, three questions define the minimum standard of custody safety.
First, demand Segregation of Duties. Never engage with a platform where the company’s operating funds are co-mingled with the asset’s custody infrastructure. The tokenization platform and the asset custodian must be independent of each other.
Second, verify the SPV and its Bankruptcy Remoteness. Confirm that the asset is held in a legally ring-fenced SPV entity that is formally documented to be insolvency-remote from the platform’s debts. This must be verified in the legal agreements, not inferred from marketing materials.
Third, ask about the Golden Record policy. Specifically, ask how the platform handles a discrepancy between its blockchain records and the official government land registry or legal title documentation. If the platform cannot answer this question clearly, that is a significant governance red flag.
Regulatory and Compliance Considerations
Custody models used in real-world asset tokenization operate within regulated frameworks. Oversight bodies may include the SEC in the United States, ESMA (European Securities and Markets Authority) in the EU, national supervisory authorities, and banking regulators applying Basel standards (international banking supervision frameworks) to custodian institutions.
Regulatory considerations include custodian licensing requirements, disclosure obligations, reporting standards, and audit obligations. Platforms operating under frameworks such as VARA (Virtual Assets Regulatory Authority) in Dubai or MiCA (Markets in Crypto-Assets Regulation) in the EU face specific custody requirements that must be documented and maintained. Regulatory alignment is essential for enforceability. For compliance architecture context, see Why Compliance Matters in Tokenized Finance and What Is VARA Regulation.
FAQ: Custody Models Used in Real-World Asset Tokenization
What custody models are used in real-world asset tokenization?
The five primary models are direct custody, third-party institutional custody using a Qualified Custodian, legal registry custody anchored in the Golden Record, SPV-based custody providing Bankruptcy Remoteness, and hybrid layered custody combining multiple safeguards with Multi-Sig or MPC architecture for digital key control.
Why are custody models important in tokenized systems?
They ensure that digital ownership corresponds to legally enforceable real-world ownership. Without structured custody infrastructure, a token is just a blockchain entry with no guaranteed real-world value behind it. Custody is the bridge between the digital key and the physical vault.
What is the difference between direct and third-party custody?
Direct custody integrates safeguarding within the tokenization provider itself, creating concentration risk. Third-party custody separates safeguarding into an independent Qualified Custodian, applying Segregation of Duties and reducing Single Point of Failure exposure significantly.
How does an SPV improve custody protection?
An SPV isolates legal ownership of the asset in a separate legal entity that is ring-fenced from the debts of the operating platform. This Bankruptcy Remoteness means that if the platform becomes insolvent, the asset inside the SPV remains protected from creditor claims.
What is the Golden Record in tokenized real estate custody?
The Golden Record is the authoritative source of truth about who owns the asset. In real estate, the government land registry holds the Golden Record. When a blockchain record and the land registry disagree, the legal registry prevails in a court of law. Platforms must actively manage Synchronization Risk to keep both records consistent.
Are custody models in real-world asset tokenization regulated?
Yes. Custody structures are subject to jurisdictional regulatory oversight including custodian licensing, disclosure requirements, reporting standards, and audit obligations. Frameworks such as VARA, MiCA, and SEC regulations each carry specific custody requirements for tokenized asset platforms.
Conclusion
Custody models used in real-world asset tokenization form the protective infrastructure layer that safeguards asset ownership and ensures enforceability. Without sound custody, the digital representation of ownership has nothing real behind it.
The five key models, from direct custody through to hybrid layered institutional architecture, differ in who holds authority, how risk is distributed, and what investor profile they serve. Institutional-grade tokenization requires at minimum Bankruptcy Remoteness through an SPV, Segregation of Duties through a Qualified Custodian, Golden Record alignment with legal registries, and Multi-Sig or MPC architecture for digital key protection.
Digital ownership representation is only as strong as the custody infrastructure protecting the underlying asset. The vault must be as secure as the key is portable.
Sources and Regulatory References
- Bank for International Settlements (BIS): https://www.bis.org
- U.S. Securities and Exchange Commission (SEC): https://www.sec.gov
- European Securities and Markets Authority (ESMA): https://www.esma.europa.eu
- World Bank Financial Sector: https://www.worldbank.org
Educational Disclaimer
This article is provided for educational purposes only and does not constitute financial, legal, or investment advice. Custody structures and regulatory requirements vary by jurisdiction and asset classification. Professional legal consultation should be obtained before engaging with any tokenized asset structure.
Last updated: March 2026
Explore Real-World Asset Tokenization
- Real-World Asset Tokenization Explained
- What Is Asset Tokenization? A Beginner-Friendly Explanation
- How Real-World Asset Tokenization Works Step by Step
- Who Verifies Real-World Assets in Tokenized Systems
- Legal Structures Behind Tokenized Real Estate
- Benefits and Risks of RWA Tokenization (cluster)
- What Is Proof of Reserve (cross-pillar)
- On-Chain Transparency Explained (cross-pillar)
- Why Compliance Matters in Tokenized Finance (cross-pillar)
- Real-World Assets Hub